
29 Dec Cloud Security Best Practices in 2022
Cloud Security Best Practices in 2022
A study by IDG on cloud computing has it that 92% of organizations’ IT environment is today on the cloud. This in part has been driven by the COVID 19 pandemic that had organizations moving to the cloud to support employees and teams working remotely.
With its increased flexibility, productivity and reduced costs, the cloud has become the most sought-after option for businesses around the world.
92% of organizations’ IT environment is today on the cloud.
Nevertheless, it’s crucial to set high cloud security standards for businesses to survive in a highly disruptive digitally connected environment. Sometimes, a case of cloud misalignment or an issue with your cloud configuration can cause massive damage to organizations from data leakage and breaches, giving malicious actors access to highly sensitive data.
This makes adopting cloud security best practices a critical responsibility for organizations to prevent unauthorized access, while keeping their data and applications in the cloud secure from current and emerging cybersecurity threats.
In a 12-month timeframe, organizations lost ~$6.2 million to cloud account compromises.
What is cloud security?
Cloud security simply means procedures and technology that secure cloud computing environments against both external and insider cybersecurity threats. The security measures are configured such that it protects cloud data, supports regulatory compliance and protects customers’ privacy. Apart from this, authentication rules for individual users and devices can also be set.
Cloud security simply means procedures and technology that secure cloud computing environments against both external and insider cybersecurity threats
Why is cloud security important?
When businesses make a transition to the cloud, robust cloud security is critical. As security threats constantly evolve, becoming more sophisticated with time, your cloud environment is constantly at risk just as your on-premises environment.
For this reason, it is critical to use the services of a managed cloud service provider to build best-in-class security that is customized for your business infrastructure. With cloud security, you get:
Centralized protection and security: Cloud security centralizes protection managing security on numerous devices and endpoints that can be otherwise difficult to manage. When security is centrally managed, it streamlines monitoring of network events and resuts in fewer software and policy updates. It makes the management of disaster recovery plans as well.
Dependability: When cloud security measures are in place, it allows users safe access to data and applications within the cloud. Organizations are increasingly realizing the business benefits of moving their systems to the cloud. The cloud allows organizations to operate at scale, reduce technology costs and use agile systems that give them a competitive advantage.
However, at the center of it needs to be cloud security, as well as the data, systems and applications that are protected from data theft, leakage, corruption and deletion.
Reduced manual effort: When you move to a reputable cloud managed services, it means you no longer need to worry about manual security configurations and constant security updates. With the cloud, all security adminsitration happens at one place, and is fully managed on your behalf.
Lowered costs: Cloud storage eliminates the need to invest in dedicated hardware. Not only does this reduce capital expenditure, administrative overheads are reduced as well. As organizations adopt cloud and choose a cloud service provider (CSP), not being fully aware of the risks involved exposes it to myriad o of commercial, financial, technical, legal, and compliance risks. Cloud computing, much like a traditional data center, runs software, and software can have vulnerabilities that adversaries try to exploit. But unlike in a traditional data center, where the consumer needs to employ personnel to ensure network security, in the case of cloud computing, the responsibility of mitigating risks arising from these vulnerabilities is shared between the CSP and the cloud consumer.
So, the responsibiity is shared and the consumer needs to carry out their tasks and ensure the CSP meets their responsibilities.
So, what are the critical cloud vulnerabilities businesses need to address:
- Reduced visibility and control of the consumer
When organizations transition assets or operations to the cloud, they often tend to lose visibility over the assets/operations. When the CSP becomes responsible for policy and infrastructure changes as external cloud services are used; it creates a shift of responsibility. But the actual change depends on the cloud service model businesses adopt – which is a massive change for organizations with regard to security monitoring and logging. The ensuing confusion if not addressed by the two players can create critical vulnerabilities in the business’ security infrastructure.
- Unauthorized use due to on-demand self service
While the cloud makes it easy to provision new services, with on-demand self service provisioning features of the cloud that enable an organization’s personnel to provision additional services from the agency’s CSP without IT consent; it could lead to the practice of shadow IT. Shadow IT refers to the practice of using software in an organization that is not supported by the organization’s IT department. They present considerable risk to the organization’s security and could result in an increase in malware infections or data exfiltration since the organization is unable to protect resources it does not know about. Vulnerabilities can also be caused by the decrease in the organization’s visibility and control of its network and data.
- When multi-tenant setup fails
Exploiting system and software vulnerabilities in your cloud infrastructure, platforms or applications supporting a multi-tenant setup can cause failure in maintaining separation among tenants. This failure can expose vulnerabilities and expose the organization to attacks from outsiders. Multi-tenancy increases attack surface and can cause data leakages if separation controls fail.
- Insecure APIs
CSPs expose application programming interfaces (APIs) that customers can use to manage and interact with cloud services. Since they are accessible via the internet, they expose the organization broadly to potential exploitation. Cyber attackers often check for vulnerable points in management APIs. And if any are discovered, they can be turned into successful attacks, and the organization’s cloud assets can be compromised.
- Incomplete data deletion
When consumers have reduced visibility into where their data is physically stored, it increases the possibility of an attack. In this scenario, consumers have a reduced ability to verify the secure deletion of their data. The raises risks because when data is spread over several storage devices in a multi-tenancy environment, its remnants could be accessible to attackers.
- Misconfigured cloud storage
Nearly 70 million records were stolen or leaked in just 2018 due to misconfigured cloud storage buckets – a report by Symantec. Cloud storage misconfiguration can fast escalation into a major cloud debacle for an organization and its customers. Some types of misconfigurations are – group misconfigurations and lack of access restrictions.
- Compliance violations
Having rules to determine who can access data and what they can do is a critical priority. A lack of access control poses risks as it can be difficult to keep track of who can access what on the cloud. Compliance ensures that organizations know the details about their data storage and access control. When assets are moved to the public cloud, it does not ensure regulatory compliance – which usually makes compliance a challenge. Though the “shared responsibility model” means they down the cloud security, data security is the organization’s responsibility. Though privacy mandates like GDPR apply to cloud computing and if there’s personally identifiable information (PII) management, moving to the cloud could make compliance an issue.
- Insider security threats
Companies that do not have control over how employees use cloud computing services could lost control of their data assets and create vulnerabilities and insider security threats. Insiders can directly access sensitive data in the cloud infrastructure without much hassle, which can lead to the loss of intellectual property and proprietary information. This has clear implications for the organization.
- Improper access management
One of the most common cloud security risks, poor access management, involves breaches involving web applications, and stolen and lost credentials. This is the most widely used tool by attackers for several years. With access management, users can perform tasks that they are authorized to. Authorization is the process of verifying what an individual has access to. While this is the standard access management issue – managing a distributed workforce or user password fatigue, some of the cloud-specific challenges include inactive assigned users, multiple admin accounts, improper user and service provisioning and bypassing enterprise access management controls.
- Contractual breaches
Cloud service contract should include the rights to review, monitor and audit reports.
Contracts restrict who is authorized to access the data, where it can be used, where and how it can be stored. When employees move restricted data into the cloud without authorization, it could violate business contracts and could result in legal action against your enterprise. Similarly, confidentiality breaches, and general leakage of data could result is your business suffering from lawsuits.
What can business do to overcome these challenges and get an edge over malicious actors?
Let’s understand some of the best cloud security practices to keep your cloud environment secure.
- Understandwhat the sharedresponsibility model is
While the enterprise is solely responsible for all security issues in a private data center, on the cloud, the CSP assumes some of the responsibility. This is the shared responsibility model. Leading IaaS and PaaS vendors like AWS and Microsoft Azure have documents for customers where specific responsibilities lie according to different types of deployment.
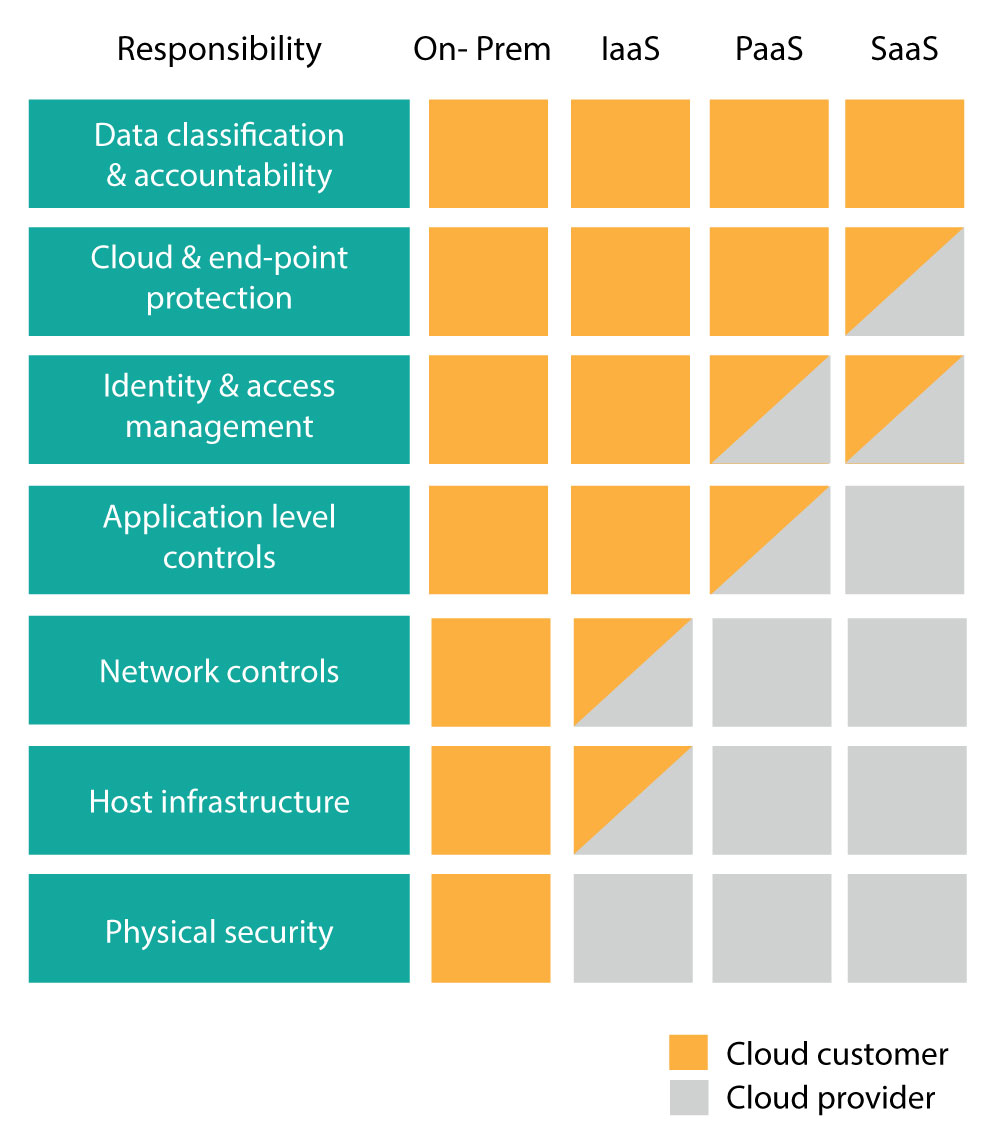
Source: Microsoft
Enterprises considering popular CSPs must review their policies about shared security and understand who is handling what in cloud security. This prevents miscommunication and gives all players the clarity needed to keep your cloud infrastructure secure.
- Clarify your cloud security questions
Ask your CSP detailed questions about the security measures and processes in place. While it is easy to assume leading CSP providers have security handled, the truth is security methods vary significantly from vendor to vendor.
Some questions to ask are:
- Where are the provider’s servers located?
- Does the provider encrypt data while in transit and at rest?
- Which roles or individuals from the provider’s side have access to data stored in the cloud?
- What are the provider’s authentication methods?
- What compliance requirements do the provider support?
- What is the protocol for suspected security incidents?
- What is the provider’s disaster recovery plan?
- Measure providers have in place to protect various access components?
- What level of technical support is the provider willing to provide?
What were the results of the provider’s recent penetration tests?
- Deploy an IAM solution
Unauthorized access is one of the biggest threats to cloud security. A high-quality identity and access management (IAM) solution can mitigate access-related threats to a great extent. Organizations must look for an IAM solution that allows them to define access policies based on least privilege. Role-based permission capabilities should also be a deciding factor. Additionally, multi-factor authentication (MFA) can reduce the risk of malicious entities gaining information that’s sensitive, even if they have a username and password.
- Enforce cloud security policies
Maintaining written guidelines that detail who can use cloud services, how they can be used and which data can be stored is a cloud security best practice. The guideline must also include the specific security technologies which employees can use to protect data and applications in the cloud. Security staff can use automated solutions to ensure all employees follow the policy and in certain cases, the CSP would be following certain policy enforcement practices that would meet the organization’s needs. Third-party solutions are an option as well. Zero trust is one such technology that offers control over policy enforcement.
- Data encryption
When using a public cloud storage system, it’s always a best practice to encrypt that data. Data must be encrypted at rest and while in transit as well. Some CSPs provide encryption and key management services and certain third-party and traditional software companies offer encryption as well. Figure out an encryption process that works seamlessly with existing work processes and eliminate the need for end users to take any extra steps to comply with the company’s encryption policies.
- Secure APIs
You can also follow the cloud security best practice of developing APIs with strong authentication, encryption, activity monitoring and access control.APIs must be secured. When you conduct penetration tests targeting your API endpoints and get a secure code review done, it will best ensure you have a secure software development lifecycle (SDLC) that ensures you develop secure applications and APIs. For data in transit, consider the SSL/TLS encryption. For stronger authentication controls, implement multi-factor authentication with schemas such as one-time passwords to ensure strong authentication control.
- Intrusion prevention and detection systems
Intrusion prevention and detection systems (IDPS) are efficient cloud security tools and are a critical cloud security best practice for organizations. The system monitors, analyzes and responds to network traffic on your premises and cloud environments. If there’s a signature-base
- Check compliance requirements
Businesses in certain geographies or those who store data in certain regions may also have compliance requirements from state or local governments. When organizations in retail, healthcare and financial services collect personally identifiable information (PII), they face strict regulations on customer privacy and data security. There, organizations need to review their specific compliance requirements and make sure the CSP can deliver on their security needs.
- Endpoint security
When you use a cloud service, the need for strong endpoint security is critical. Here, you need to revisit existing strategies and ensure the current protective measures in place can take up evolving threats. And in-depth defense strategy that includes protection with firewalls, anti-malware, intrusion detection and access control has been how endpoint security is managed. However, it is inadequate amid today’s rising cybersecurity challenges. Here, endpoint detection and response (EDR) tools or endpoint protection platforms (EPP) can help.
- Enable security logs
Together with conducting audits, organizations must enable logging features for their cloud solutions. With logging, systems admins can track which users are making changes to the environment. This process would be a challenge to manually manage. If attackers gain access and make changes, the logs would track their activities so it can be remediated. Logging can fix misconfiguration issues as well, and effective logging capabilities can help to identify vulnerabilities, which can be corrected in the future. With logging, the administrators can also identify those who have more access than required and changes can be made.
- Control unmanaged devices
Cloud services provide access from anywhere with an internet connection. In this context, access from unmanaged devices like a personal phone could create a blind spot for your security. When downloads to unmanaged devices are blocked with security verification, it keeps the environment more secure.
- Consider a cloud security solution
Several companies offer solutions and services specially designed to enhance cloud security. So, when an organization’s internal staff does not have the expertise or if the existing support does not cover cloud environments, organizations must take the help of a third-party expert. Cloud access security brokers (CASB) are tools built exclusively to ensure cloud security policies. They have become greatly popular with more organizations moving to the cloud. They are especially useful when organizations use a multi-cloud environment that involves different CSPs.
- Audits and penetration testing
Running penetration tests determine whether existing cloud security efforts are sufficient to protect data and applications. Regular audits too, which includes an analysis of all security vendors’ capability, is a cloud security best practice to follow. Access logs should be audited so that it ensures that only appropriate and authorized personnel are accessing sensitive data and applications in the cloud.
- Give your staff the necessary training
Organizations must train staff on how to spot cybersecurity threats and how to respond in case of an attack. The training should include basic security knowledge like how to create a strong password and identify possible social engineering attacks as well as more advanced topics like risk management. Staff also need to know the risks of shadow IT and organizations need to give specialized training for their security staff.
Final thoughts
Concerns about security should not stop organizations from using public cloud services. Strong cloud security relies on having the right tools in place and by following cloud security best practices, businesses can minimize risks and take advantage of cloud computing.
